Computer Network Architecture
- A Computer Network architecture gives an blueprint of how the communication network can be designed, and how will it work.
- Computer Network architecture is the design of a communications network.
- It is a framework for the specification of a network's physical components and their functional organization and configuration.
- In telecommunication, the specification of a network
architecture may also
include a detailed
description of products and services delivered
via a communications network, as well as detailed rate and billing structures under which services
are compensated.
- The network architecture of the Internet is predominantly expressed by its use of the Internet Protocol Suite, rather than a specific model for interconnecting networks or nodes in the network, or the usage of specific types of hardware link.
Types of Network Architecture
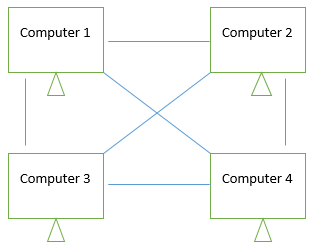
Peer-to-Peer Architecture
In a peer-to-peer network, tasks are allocated to every device on the network. Furthermore, there is no real hierarchy in this network, all computers are considered equal and all have the same abilities to use the resources available on this network. Instead of having a central server which would act as the shared drive, each computer thats connected to this network would act as the server for the files stored on it.
Advantages of a peer-to-peer network
- Does not require a dedicated server which means its less costly.
- If one computer stops working, the other computers connected to the network will continue working.
- Installation and setup is quite painless because of the built-in support in modern operating systems.
Disadvantages of a peer-to-peer network
- Security and data backups are to be done to each individual computer.
- As the numbers of computers increases on a P2P network... performance, security, and access becomes a major headache.
Client/Server Architecture
In a client/server network, a centralized, really powerful computer(server) acts as a hub in which other computers or workstations(clients) can connect to. This server is the heart of the system, which manages and provides resources to any client that requests them.
Advantages of a client/server network
- Resources and data security are controlled through the server.
- Not restricted to a small number of computers.
- Server can be accessed anywhere and across multiple platforms.
Disadvantages of a client/server network
- Can become very costly due to the need of a server as well as networking devices such as hubs, routers, and switches.
- If and when the server goes down, the entire network will be affected.
- Technical staff needed to maintain and ensure network functions efficiently.

Comments
Post a Comment
Please do not post any spam link in comment box